GhostBear: How to Hide Your VPN From DPI
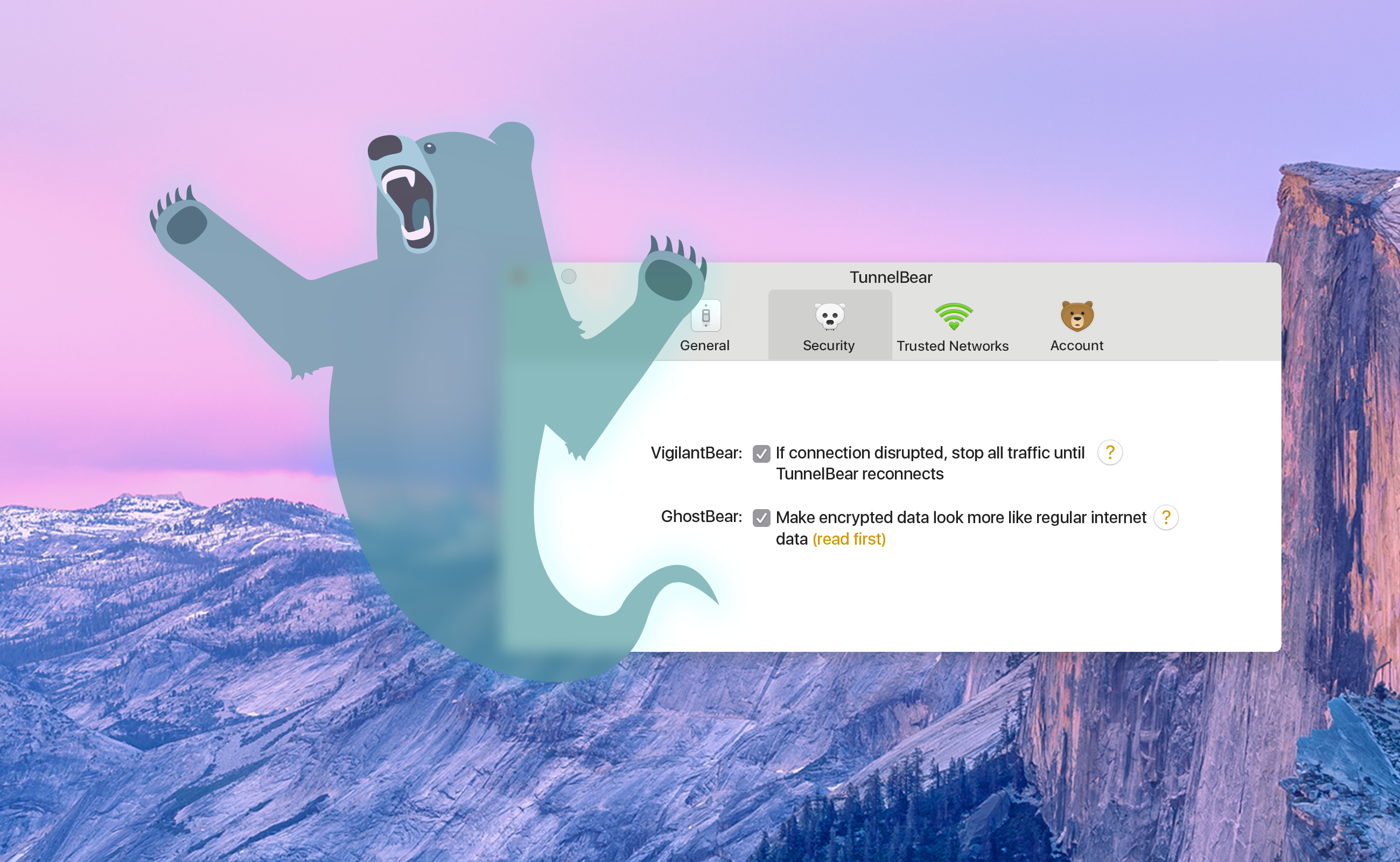
In our ongoing effort to stay transparent and open, we’d like to explain an often misunderstood feature of TunnelBear VPN. If you look in the “Preferences” drop-down of your TunnelBear app, you’ll find a checkbox that turns GhostBear on and off. This feature helps disguise your encrypted data by making it “look more like regular internet data”. It’s still encrypted, but if someone decides to take a closer look at your data, it'll be harder for them to see that you're using a VPN to encrypt your traffic.
We know what you’re thinking, “Why would I want to hide my traffic a second time? Isn’t encrypted data enough to keep my browsing private?”
DPI - how ISPs can tell you’re using a VPN
DPI is a tool used to classify and identify types of data. ISPs, Government agencies, and a host of other people, are the ones that decide to use it for “good” or “bad” reasons. For example, DPI can be used to do everything from network performance tests to stopping people from communicating outside their country’s borders.
What DPI does, is analyze the types of internet traffic people use. When you download something from a secure website, like a photo or a video, DPI can be used to see that the packets of information you’re sending and receiving are HTTPS traffic. If you send an email, the people using DPI will see SMTP, POP3 or IMAP traffic.
Organizations that want to target VPN traffic have to identify its unique signature with DPI first, then they can slow down, re-route or even block all VPN traffic on their network. Using DPI is an inexpensive and easy way for organizations to monitor their networks for unwanted traffic.
GhostBear makes your VPN vanish, sometimes
When you turn GhostBear on, it changes your VPN traffic signature to look like a different kind of traffic. It’s still encrypted VPN traffic, but if someone were to use DPI on it, all they would see is regular internet data. To do this, GhostBear uses a technology called Obfsproxy. Originally designed to work alongside Tor, Obfsproxy can be used as a standalone software that changes traffic signatures to look like traffic that isn’t normally blocked by DPI.
Obfsproxy alters a number of identifying features like how big a packet is or the order that they’re sent in. It can add or remove data to a packet by “padding” or “trimming” them into sizes that are less recognizable.
How do I know when to use GhostBear?
Unless you live in a place with very strict internet rules, you might never need to turn the feature on. GhostBear has been known to help people in Turkey, Iran and China to get around Government controlled firewalls. These firewalls use DPI to block VPN traffic in an attempt to stop people from accessing foreign news, social media and many other sites.
DPI isn’t just for government censorship though. Many airports use it on their WiFi networks and more and more University campuses are using it to block traffic that slows down school networks.
So, to answer the question, when you’re having trouble connecting to websites or services that are being blocked by a firewall, GhostBear can help. But, some clients have experienced dips in speed because obfsproxy adds an extra layer of processing.
The future of GhostBear
As threats to privacy evolve, so does TunnelBear. In the coming months we’ll be upgrading GhostBear to increase its effectiveness at cloaking VPN traffic as well as making changes to the way traffic is routed between our servers.
These changes should increase speeds and make your VPN harder to detect.
GhostBear helps open the internet on heavily restricted networks
As DPI is adopted by more organizations to monitor and control traffic, tools like GhostBear become more important to help people stay connected to the world. Disguising your VPN traffic to get through firewalls can help you secure your privacy, but GhostBear should only be used when you find yourself on a restricted network.
If you’d like to try GhostBear, you can download TunnelBear for your Android, Mac or Windows devices. To turn the option on, head to settings or preferences, security, then tap the GhostBear check box. Be sure to turn TunnelBear off before you start GhostBear or it won’t run properly.
Happy tunneling!